DevOps | InfoSec
Akeyless: The Leading HashiCorp Vault Alternative
In this video blog, Sam Gabrail explains why Akeyless leads over HashiCorp Vault, with features like automated rotation and universal identity.
DevOps | InfoSec
In this video blog, Sam Gabrail explains why Akeyless leads over HashiCorp Vault, with features like automated rotation and universal identity.
DevOps | InfoSec
DevOps | InfoSec
DevOps | InfoSec

InfoSec
The Role of Secrets Management in a Comprehensive Zero Trust StrategyThis blog explores the critical role of secrets management in implementing a Zero Trust strategy, highlighting how it protects against common cybersecurity threats and enhances overall security infrastructure.

What is CAS integration? Why does it matter for businesses and their cybersecurity strategies? Read here to find out all you need to know.

Technical Definitions
What is HSM Integration?HSM Integration refers to the process of incorporating a Hardware Security Module (HSM) into an organization’s IT and security infrastructure. HSMs are physical devices designed to secure digital keys and perform cryptographic operations, such as encryption, decryption, and digital signing, in a tamper-resistant environment. This integration is pivotal for enhancing the security of sensitive data […]
DevOps | Security
Akeyless DFC 101—A Zero-Knowledge ApproachAkeyless DFC™ allows you to retain full ownership of your data while operating in a SaaS model. Take a peek under the hood to see how DFC keeps your data secure.

News
Are you prepared for Google’s 90-day validity period on TLS certificates?Are you prepared for Google's 90-day validity period on TLS certificates? Learn what's to come and how to prepare.
Technical Definitions
What is Transparent Data Encryption (TDE)?What is Transparent Data Encryption (TDE)? An essential security feature for databases, designed to encrypt data at rest. Read more.

Security
Secrets Management in the Age of AI Cybercrime: Safeguarding Enterprises from Emerging ThreatsAI is not merely a tool for convenience and efficiency; it's reshaping the landscape of cyber warfare. Learn why Secrets Management is crucial to keeping your enterprise safe.

Technical Definitions
What is Certificate Provisioning?What is Certificate Provisioning? Obtaining, deploying, and managing digital certificates within ab IT infrastructure. Read more.

Technical Definitions
What is Tokenization?What is tokenization? A security technique to protect sensitive information like financial details and personal identifiers. Read more.

News | Product Updates
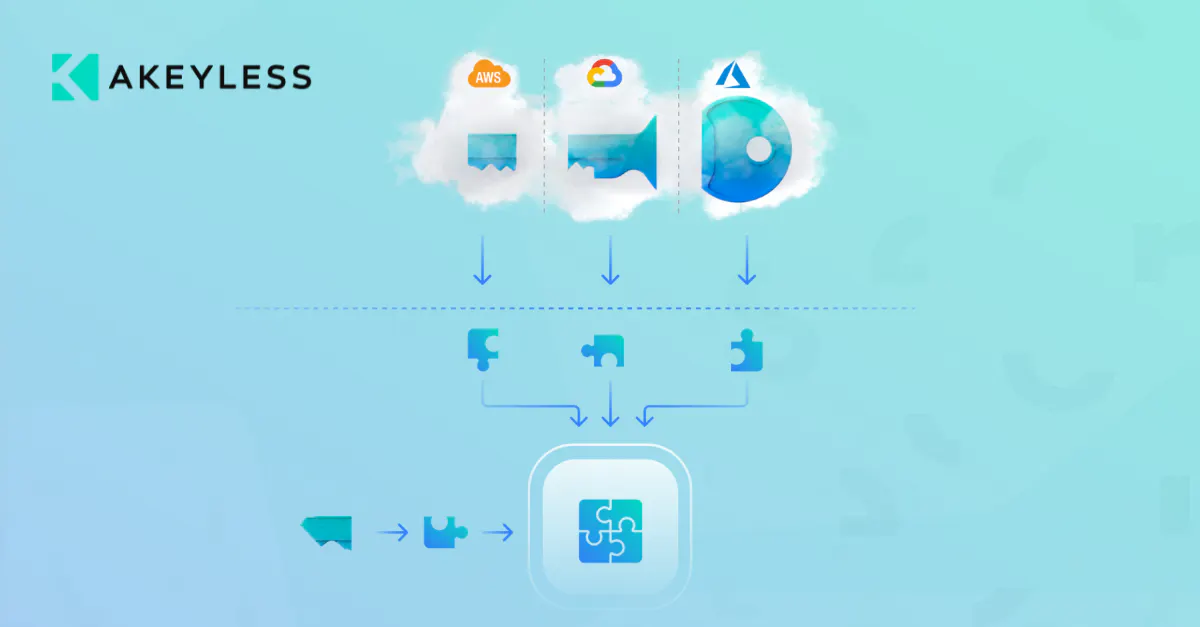
Enhancing Kubernetes Secrets Management with Akeyless and CSI Driver IntegrationExplore how Akeyless Vaultless Secrets Management integrates with the Kubernetes Secrets Store CSI Driver to enhance security and streamline secrets management in your Kubernetes environment.

Technical Definitions
What is Certificate Storage?What is Certificate Storage? Certificate storage refers to the secure location where digital certificates are kept. Read more.

Technical Definitions
What is Managing Secrets?Managing secrets involves securely orchestrating a variety of digital authentication credentials, crucial for safeguarding access to applications, services, and critical systems. These credentials, commonly referred to as ‘secrets,’ encompass a wide range of credentials, certificates, and keys. This includes passwords and tokens utilized by individuals, as well as API keys and certificates generated and managed […]